Take into consideration how a lot of the world depends on the web. The federal government, navy, academia, well being care trade, and personal trade not solely acquire, course of, and retailer unprecedented quantities of knowledge in our on-line world — in addition they depend on essential infrastructure programs in our on-line world to carry out operations and ship companies.
An assault on this infrastructure couldn’t solely threaten buyer information or a enterprise’s backside line — it might additionally threaten a nation’s safety, financial system, and public security and well being.
Contemplating its significance, we’ve compiled this final information on cybersecurity. Beneath, we’ll discuss what cybersecurity is strictly, learn how to shield your programs and information from assaults, and what assets to comply with to remain up-to-date with rising traits and expertise associated to cybersecurity.
What’s cybersecurity?
Cybersecurity is the observe of securing information, gadgets, packages, networks, and programs in opposition to assaults. These assaults, often called cyber assaults, are designed to use vulnerabilities in a person’s machine or enterprise’s system with a purpose to disrupt, disable, destroy, or management their information or infrastructure.
Good cybersecurity includes a number of layers of safety throughout the info, gadgets, packages, networks, and programs of an enterprise. A mixture of expertise and greatest practices can present an efficient protection in opposition to the frequently evolving and rising threats of our on-line world.
These threats embrace phishing, malware, ransomware, code injections, and extra. The affect can fluctuate relying on the scope of the assault. A cyber assault may outcome within the attacker making unauthorized purchases with a person’s bank card data, or erasing a complete system after injecting malware into a company’s code base.
Whereas even the most effective cybersecurity can’t defend in opposition to each kind or occasion of assault, it will possibly assist to reduce the dangers and affect of such assaults.
Sorts of Cybersecurity
Cybersecurity is a broad time period that may be damaged down into extra particular subcategories. Beneath we’ll stroll via 5 main varieties of cybersecurity.
Software Safety
Software safety, also referred to as AppSec, is the observe of creating, including, and testing safety features inside internet purposes with a purpose to shield them in opposition to assaults. Vulnerabilities, safety misconfigurations, and design flaws could be exploited and end in malicious code injections, delicate information publicity, system compromise, and different destructive impacts. HubSpot’s Content material Hub offers a free internet utility firewall (WAF) that may shield your website and content material from malicious assaults.
AppSec is among the most vital varieties of cybersecurity as a result of the appliance layer is essentially the most weak. In accordance with Imperva analysis, almost half of knowledge breaches over the previous a number of years originated on the internet utility layer.
Cloud Safety
Cloud safety is a comparatively current kind of cybersecurity. It’s the observe of defending cloud computing environments in addition to purposes operating in and information saved within the cloud.
Since cloud suppliers host third-party purposes, companies, and information on their servers, they’ve safety protocols and options in place — however purchasers are additionally partially accountable and anticipated to configure their cloud service correctly and use it safely.
Essential Infrastructure Safety
Essential infrastructure safety is the observe of defending the essential infrastructure of a area or nation. This infrastructure consists of each bodily safety and cyber networks, programs, and belongings that present bodily and financial safety or public well being and security. Consider a area’s electrical energy grid, hospitals, visitors lights, and water programs as examples.
A lot of this infrastructure is digital or depends on the web ultimately to operate. It’s subsequently inclined to cyber assaults and should be secured.
Web of Issues (IoT) safety
Web of Issues safety, or IoT safety, is the observe of defending nearly any machine that connects to the web and may talk with the community independently of human motion. This consists of child screens, printers, safety cameras, movement sensors, and a billion different gadgets in addition to the networks they’re linked to.
Since IoT gadgets acquire and retailer private info, like an individual’s identify, age, location, and well being information, they may help malicious actors steal folks’s identities and should be secured in opposition to unauthorized entry and different threats.
Community Safety
Community safety is the observe of defending laptop networks and information in opposition to exterior and inner threats. Id and entry controls like firewalls, digital personal networks, and two-factor authentication may help.
Community safety is often damaged down into three classes: bodily, technical, and administrative. Every of these kinds of community safety is about making certain solely the appropriate folks have entry to community elements (like routers), information that’s saved in or transferred by the community, and the infrastructure of the community itself.
Cybersecurity Phrases to Know
Cybersecurity is a really intimidating subject, not in contrast to cryptocurrency and synthetic intelligence. It may be arduous to grasp, and, frankly, it sounds form of ominous and sophisticated.
However worry not. We’re right here to interrupt this subject down into digestible items that you may rebuild into your personal cybersecurity technique. Bookmark this put up to maintain this useful glossary at your fingertips.
Right here’s a complete checklist of basic cybersecurity phrases you must know.
Authentication
Authentication is the method of verifying who you might be. Your passwords authenticate that you just actually are the one who ought to have the corresponding username. Whenever you present your ID (e.g., driver’s license, and so forth), the truth that your image usually seems such as you is a approach of authenticating that the identify, age, and deal with on the ID belong to you. Many organizations use two-factor authentication, which we cowl later.
Backup
A backup refers back to the technique of transferring vital information to a safe location like a cloud storage system or an exterior arduous drive. Backups allow you to get well your programs to a wholesome state in case of a cyber assault or system crash.
Conduct Monitoring
Conduct monitoring is the method of observing the actions of customers and gadgets in your community to acknowledge any potential safety occasions earlier than they happen. Actions should not solely be noticed but additionally measured in opposition to baselines of regular habits, traits, and organizational insurance policies and guidelines.
For instance, you may monitor and observe when customers log in and log off, in the event that they request entry to delicate belongings, and what web sites they go to. Then say a person tries to log in at an uncommon time, just like the nighttime. In that case, you possibly can establish that as uncommon habits, examine it as a possible safety occasion, and finally block that log in try for those who suspect an assault.
Bot
A bot, quick for robotic, is an utility or script designed to carry out automated and repetitive duties. Some bots have authentic functions, like chatbots that reply generally requested questions on a web site. Others are used for malicious functions, like sending spam emails or conducting DDoS assaults. As bots turn into extra subtle, it will get tougher to inform the distinction between good bots and unhealthy bots and even bots from human customers. That’s why bots pose an ever-growing menace to many people and organizations.
CIA Triad
The CIA triad is a mannequin that can be utilized to develop or consider a company’s cybersecurity programs and insurance policies.
The CIA triad refers to confidentiality, integrity, and availability. In observe, this mannequin ensures information is disclosed solely to approved customers, stays correct and reliable all through its lifecycle, and could be accessed by approved customers when wanted despite software program failures, human error, and different threats.

Information Breach
A information breach refers back to the second a hacker positive factors unauthorized entry or entry to an organization’s or a person’s information.
Digital Certificates
A digital certificates, also referred to as an identification certificates or public key certificates, is a sort of passcode used to securely alternate information over the web. It’s basically a digital file embedded in a tool or piece of {hardware} that gives authentication when it sends and receives information to and from one other machine or server.
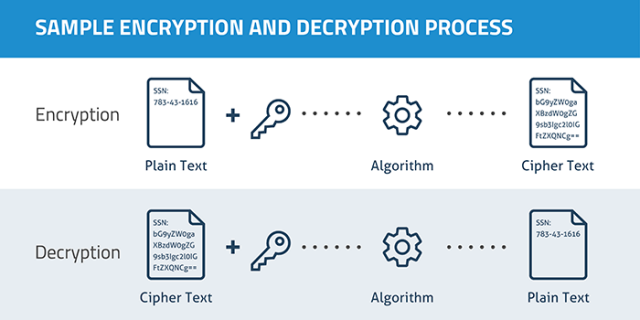
Encryption
Encryption is the observe of utilizing codes and ciphers to encrypt information. When information is encrypted, a pc makes use of a key to show the info into unintelligible gibberish. Solely a recipient with the right key is ready to decrypt the info. If an attacker will get entry to strongly encrypted information however doesn’t have the important thing, they aren’t in a position to see the unencrypted model.
HTTP and HTTPS
Hypertext Switch Protocol (HTTP) is how internet browsers talk. You’ll most likely see an http:// or https:// in entrance of the web sites you go to. HTTP and HTTPS are the identical, besides HTTPS encrypts all information despatched between you and the online server — therefore the “S” for safety. Right this moment, almost all web sites use HTTPS to enhance the privateness of your information just like the free SSL supplied by the free Content material Hub.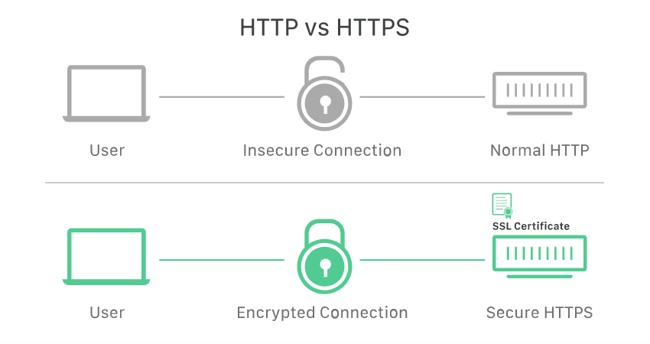
Vulnerability
A vulnerability is a spot of weak point {that a} hacker may exploit when launching a cyber assault. Vulnerabilities is perhaps software program bugs that have to be patched, or a password reset course of that may be triggered by unauthorized folks. Defensive cybersecurity measures (like those we discuss later) assist guarantee information is protected by placing layers of protections between attackers and the issues they’re attempting to do or entry.
Sorts of Cyber Assaults
- Password Guessing Assault
- Distributed Denial of Service (DDoS) Assault
- Malware Assault
- Phishing Assault
- Man-in-the-Center (MitM) Assault
- Cross Website Scripting Assault
- SQL Injection Assault
A cyber assault is a deliberate and usually malicious intent to seize, modify, or erase personal information. Cyber assaults are dedicated by exterior safety hackers and, generally, unintentionally by compromised customers or workers. These cyber assaults are dedicated for quite a lot of causes. Some are in search of ransom, whereas some are merely launched for enjoyable.
Beneath we’ll briefly go over the most typical cyber threats.
1. Password Guessing (Brute Pressure) Assault
A password guessing (or “credential stuffing”) assault is when an attacker frequently makes an attempt to guess usernames and passwords. This assault will usually use identified username and password mixtures from previous information breaches.
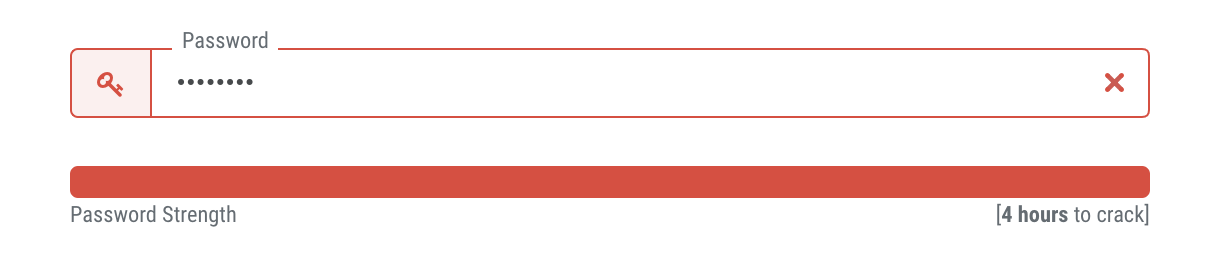
An attacker is profitable when folks use weak passwords or use the password between totally different programs (e.g., when your Fb and Twitter password are the identical, and so forth). Your greatest protection in opposition to this type of assault is utilizing robust passwords and avoiding utilizing the identical password in a number of locations in addition to utilizing two issue authentication, as we discuss later.)
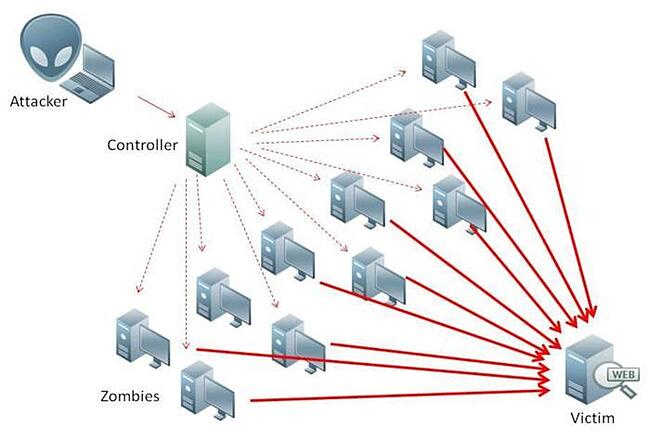
2. Distributed Denial of Service (DDoS) Assault
A distributed denial of service (DDoS) assault is when a hacker floods a community or system with a ton of exercise (resembling messages, requests, or internet visitors) with a purpose to paralyze it.
That is usually achieved utilizing botnets, that are teams of internet-connected gadgets (e.g., laptops, gentle bulbs, sport consoles, servers, and so forth) contaminated by viruses that enable a hacker to harness them into performing many sorts of assaults.
3. Malware Assault
Malware refers to all varieties of malicious software program utilized by hackers to infiltrate computer systems and networks and acquire inclined personal information. Sorts of malware embrace:
- Keyloggers, which observe every part an individual sorts on their keyboard. Keyloggers are normally used to seize passwords and different personal info, resembling social safety numbers.
- Ransomware, which encrypts information and holds it hostage, forcing customers to pay a ransom with a purpose to unlock and regain entry to their information.
- Spyware and adware, which screens and “spies” on person exercise on behalf of a hacker.
Moreover, malware could be delivered through:
- Trojan horses, which infect computer systems via a seemingly benign entry level, usually disguised as a authentic utility or different piece of software program.
- Viruses, which corrupt, erase, modify, or seize information and, at occasions, bodily injury computer systems. Viruses can unfold from laptop to laptop, together with when they’re unintentionally put in by compromised customers.
- Worms, that are designed to self-replicate and autonomously unfold via all linked computer systems which can be inclined to the identical vulnerabilities. .
4. Phishing Assault
A phishing assault is when hackers attempt to trick folks into doing one thing. Phishing scams could be delivered via a seemingly authentic obtain, hyperlink, or message.
It’s a quite common kind of cyber assault — 57% of respondents in a third-party survey stated their group skilled a profitable phishing assault in 2020, up from 55% in 2019. And the affect of profitable phishing assaults vary from lack of information to monetary loss.
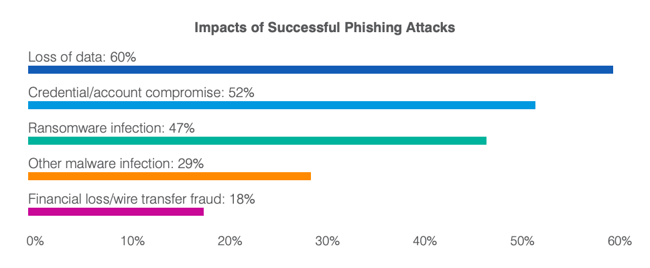
Phishing is often achieved over electronic mail or via a pretend web site; it’s also referred to as spoofing. Moreover, spear phishing refers to when a hacker focuses on attacking a specific individual or firm, resembling stealing their identification, as an alternative of making extra general-purpose spams.
5. Man-in-the-Center (MitM) Assault
A Man-in-the-Center (MitM) assault is when an attacker intercepts communications or transactions between two events and inserts themselves within the center. The attacker can then intercept, manipulate, and steal information earlier than it reaches its authentic vacation spot. For instance, say a customer is utilizing a tool on public WiFi that hasn’t been secured correctly, or in any respect. An attacker might exploit this vulnerability and insert themselves between the customer’s machine and the community to intercept login credentials, fee card info, and extra.
This kind of cyber assault is so profitable as a result of the sufferer has no thought that there’s a “man within the center.” It simply looks as if they’re looking the online, logging into their financial institution app, and so forth.
%20Attack-p-500.jpeg?width=650&name=605cab5ff8f386ea033ae16c_Man-in-the-Middle)%20Attack-p-500.jpeg)
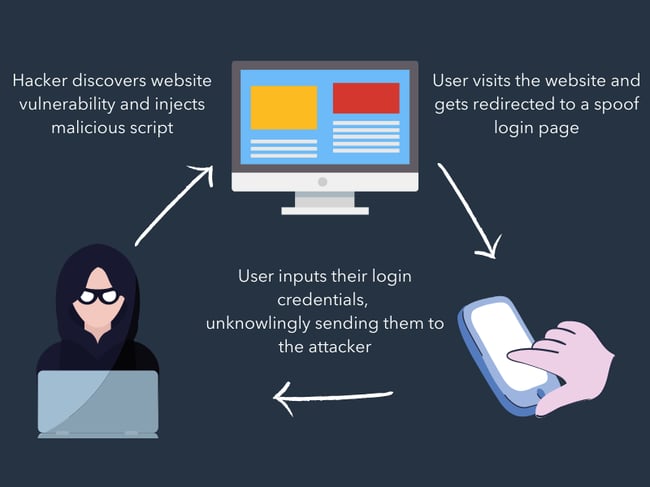
6. Cross Website Scripting Assault
A cross website scripting assault, or XSS assault, is when an attacker injects malicious code into an in any other case authentic web site or utility with a purpose to execute that malicious code in one other person’s internet browser.
As a result of that browser thinks the code is coming from a trusted supply, it should execute the code and ahead info to the attacker. This info is perhaps a session token or cookie, login credentials, or different private information.
Here is an illustrated instance of an XSS assault:
7. SQL Injection Assault
An SQL injection assault is when an attacker submits malicious code via an unprotected kind or search field with a purpose to achieve the power to view and modify the web site’s database. The attacker may use SQL, quick for Structured Question Language, to make new accounts in your website, add unauthorized hyperlinks and content material, and edit or delete information.
This can be a frequent WordPress safety concern since SQL is the popular language on WordPress for database administration.
Cybersecurity Greatest Practices: How you can Safe Your Information
Cybersecurity can’t be boiled down right into a 1-2-3-step course of. Securing your information includes a mixture of greatest practices and defensive cybersecurity methods. Dedicating time and assets to each is the easiest way to safe your — and your clients’ — information.
Defensive Cybersecurity Options
All companies ought to spend money on preventative cybersecurity options. Implementing these programs and adopting good cybersecurity habits (which we focus on subsequent) will shield your community and computer systems from exterior threats.
Right here’s an inventory of 5 defensive cybersecurity programs and software program choices that may forestall cyber assaults — and the inevitable headache that follows. Take into account combining these options to cowl all of your digital bases.
Antivirus Software program
Antivirus software program is the digital equal of taking that vitamin C increase throughout flu season. It’s a preventative measure that screens for bugs. The job of antivirus software program is to detect viruses in your laptop and take away them, very like vitamin C does when unhealthy issues enter your immune system. (Spoken like a real medical skilled …) Antivirus software program additionally alerts you to doubtlessly unsafe internet pages and software program.
Be taught extra: McAfee, Norton. or Panda (without cost)
Firewall
A firewall is a digital wall that retains malicious customers and software program out of your laptop. It makes use of a filter that assesses the protection and legitimacy of every part that wishes to enter your laptop; it’s like an invisible choose that sits between you and the web. Firewalls are each software program and hardware-based.
Be taught extra: McAfee LiveSafe or Kaspersky Web Safety
Spend money on Risk Detection and Prevention
Whether or not you are utilizing the Content material Hub or a standard web site internet hosting service like WordPress, it is important to combine a software to scan and detect threats. Most content material administration programs will embrace a malware scanning and menace detection function inside the platform. However for those who use platforms like WordPress, you must spend money on a safety scanner.
Single Signal-On (SSO)
Single sign-on (SSO) is a centralized authentication service via which one login is used to entry a complete platform of accounts and software program. For those who’ve ever used your Google account to enroll or into an account, you’ve used SSO. Enterprises and companies use SSO to permit workers entry to inner purposes that comprise proprietary information.
Be taught extra: Okta or LastPass
Two-Issue Authentication (2FA)
Two-factor authentication (2FA) is a login course of that requires a username or pin quantity and entry to an exterior machine or account, resembling an electronic mail deal with, telephone quantity, or safety software program. 2FA requires customers to substantiate their identification via each and, due to that, is much safer than single issue authentication.
Be taught extra: Duo
Digital Non-public Community (VPN)
A digital personal community (VPN) creates a “tunnel” via which your information travels when getting into and exiting an online server. That tunnel encrypts and protects your information in order that it will possibly’t be learn (or spied on) by hackers or malicious software program. Whereas safe VPNs shield in opposition to spy ware, they’ll’t forestall viruses from getting into your laptop via seemingly authentic channels, like phishing or perhaps a pretend VPN hyperlink. Due to this, VPNs needs to be mixed with different defensive cybersecurity measures with a purpose to shield your information.
Be taught extra: Cisco’s AnyConnect or Palo Alto Networks’ GlobalProtect
Cybersecurity Suggestions for Enterprise
Defensive cybersecurity options gained’t work until you do. To make sure your enterprise and buyer information is protected, undertake these good cybersecurity habits throughout your group.
Require robust credentials.
Require each your workers and customers (if relevant) to create robust passwords. This may be achieved by implementing a personality minimal in addition to requiring a mixture of higher and lowercase letters, numbers, and symbols. Extra sophisticated passwords are tougher to guess by each people and bots. Additionally, require that passwords be modified recurrently.
Management and monitor worker exercise.
Inside your enterprise, solely give entry to vital information to approved workers who want it for his or her job. Prohibit information from sharing exterior the group, require permission for exterior software program downloads, and encourage workers to lock their computer systems and accounts at any time when not in use.
Know your community.
With the rise of the Web of Issues, IoT gadgets are popping up on firm networks like loopy. These gadgets, which aren’t below firm administration, can introduce danger as they’re usually unsecured and run weak software program that may be exploited by hackers and supply a direct pathway into an inner community.
“Ensure you have visibility into all of the IoT gadgets in your community. All the pieces in your company community needs to be recognized, correctly categorized, and managed. By figuring out what gadgets are in your community, controlling how they hook up with it, and monitoring them for suspicious actions, you may drastically scale back the panorama attackers are enjoying on.” — Nick Duda, Principal Safety Officer at HubSpot
Examine how HubSpot positive factors machine visibility and automates safety administration in this case research compiled by safety software program ForeScout.
Obtain patches and updates recurrently.
Software program distributors recurrently launch updates that deal with and repair vulnerabilities. Hold your software program secure by updating it on a constant foundation. Take into account configuring your software program to replace robotically so that you always remember.
Make it simple for workers to escalate points.
In case your worker comes throughout a phishing electronic mail or compromised internet web page, you need to know instantly. Arrange a system for receiving these points from workers by dedicating an inbox to those notifications or making a kind that individuals can fill out.
Cybersecurity Suggestions for People
Cyber threats can have an effect on you as a person client and web person, too. Undertake these good habits to guard your private information and keep away from cyber assaults.
Combine up your passwords.
Utilizing the identical password for all of your vital accounts is the digital equal of leaving a spare key below your entrance doormat. A current research discovered that over 80% of knowledge breaches had been a results of weak or stolen passwords. Even when a enterprise or software program account doesn’t require a powerful password, at all times select one which has a mixture of letters, numbers, and symbols and alter it recurrently.
Monitor your financial institution accounts and credit score steadily.
Assessment your statements, credit score experiences, and different essential information regularly and report any suspicious exercise. Moreover, solely launch your social safety quantity when completely mandatory.
Be intentional on-line.
Hold an eye fixed out for phishing emails or illegitimate downloads. If a hyperlink or web site seems fishy (ha — get it?), it most likely is. Search for unhealthy spelling and grammar, suspicious URLs, and mismatched electronic mail addresses. Lastly, obtain antivirus and safety software program to provide you with a warning of potential and identified malware sources.
Again up your information recurrently.
This behavior is nice for companies and people to grasp — information could be compromised for each events. Take into account backups on each cloud and bodily places, resembling a tough drive or thumb drive.
Why You Ought to Care About Cybersecurity
In accordance with a report by RiskBased Safety, there have been 3,932 information breaches reported in 2020, which uncovered over 37 billion data. Furthermore, a current research discovered that the worldwide common value of a knowledge breach amounted to 3.86 million U.S. {dollars} in 2020. Which means the price of information breaches amounted to roughly 15.2 billion {dollars} final 12 months.
Small to medium-sized companies (SMBs) are particularly in danger. You may see companies like Goal and Sears topping the headlines as prime information breach victims, but it surely’s really SMBs that hackers want to focus on.
Why? They’ve extra — and extra helpful — digital belongings than your common client however much less safety than a bigger enterprise-level firm … inserting them proper in a “hackers’ cybersecurity candy spot.”
Safety breaches are irritating and scary for each companies and customers. In a survey by Measure Protocol, roughly 86% of respondents stated that current privateness breaches within the information had impacted their willingness to share private info to some extent.
However cybersecurity is about extra than simply avoiding a PR nightmare. Investing in cybersecurity builds belief together with your clients. It encourages transparency and reduces friction as clients turn into advocates in your model.
“Everybody has a task in serving to to guard clients’ information. Right here at HubSpot, each worker is empowered to resolve for buyer wants in a secure and safe approach. We need to harness everybody’s vitality to offer a platform that clients belief to accurately and safely retailer their information.” — Chris McLellan, HubSpot Chief Safety Officer
Cybersecurity Assets
The assets beneath will assist you study extra about cybersecurity and learn how to higher equip your enterprise and group. We additionally suggest testing essentially the most standard cybersecurity podcasts and cybersecurity blogs, too.
Nationwide Institute of Requirements and Expertise (NIST)
NIST is a authorities company that promotes excellence in science and trade. It additionally accommodates a Cybersecurity division and routinely publishes guides that requirements.
Bookmark: The Pc Safety Useful resource Middle (CSRC) for safety greatest practices, known as NIST Particular Publications (SPs).
The Middle for Web Safety (CIS)
CIS is a worldwide, non-profit safety useful resource and IT group used and trusted by specialists within the subject.
Bookmark: The CIS Prime 20 Essential Safety Controls, which is a prioritized set of greatest practices created to cease essentially the most pervasive and harmful threats of right this moment. It was developed by main safety specialists from world wide and is refined and validated yearly.
Cybrary
Cybrary is an internet cybersecurity training useful resource. It gives largely free, full-length instructional movies, certifications, and extra for all types of cybersecurity matters and specializations.
Bookmark: The Licensed Data Techniques Safety Skilled (CISSP) 2021, which is the newest course for info safety professionals. Incomes this “gold commonplace” of cybersecurity certifications will set you other than different info safety professionals.
The Cyber Readiness Institute
The Cyber Readiness Institute is an initiative that convenes enterprise leaders from totally different sectors and areas to share assets and information to finally advance the cyber readiness of small and medium-sized companies.
Bookmark: The Cyber Readiness Program, which is a free, on-line program designed to assist small and medium-sized enterprises safe their information, workers, distributors, and clients in opposition to right this moment’s commonest cyber vulnerabilities.
Signing Off … Securely
Cyber assaults could also be intimidating, however cybersecurity as a subject doesn’t need to be. It’s crucial to be ready and armed, particularly for those who’re dealing with others’ information. Companies ought to dedicate time and assets to defending their computer systems, servers, networks, and software program and may keep up-to-date with rising tech.
Dealing with information with care solely makes your enterprise extra reliable and clear — and your clients extra loyal.
Word: Any authorized info on this content material isn’t the identical as authorized recommendation, the place an legal professional applies the regulation to your particular circumstances, so we insist that you just seek the advice of an legal professional for those who’d like recommendation in your interpretation of this info or its accuracy. In a nutshell, chances are you’ll not depend on this as authorized recommendation or as a suggestion of any explicit authorized understanding.
Editor’s word: This put up was initially revealed in February 2019 and has been up to date for comprehensiveness.


